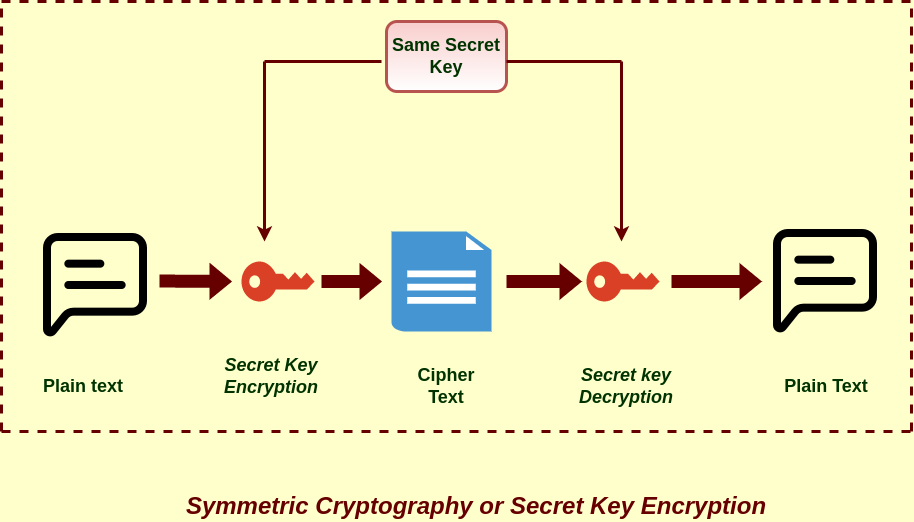
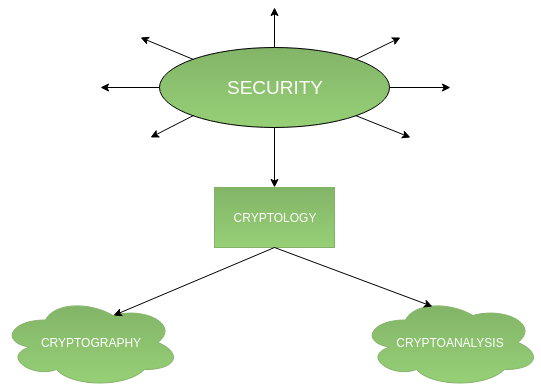
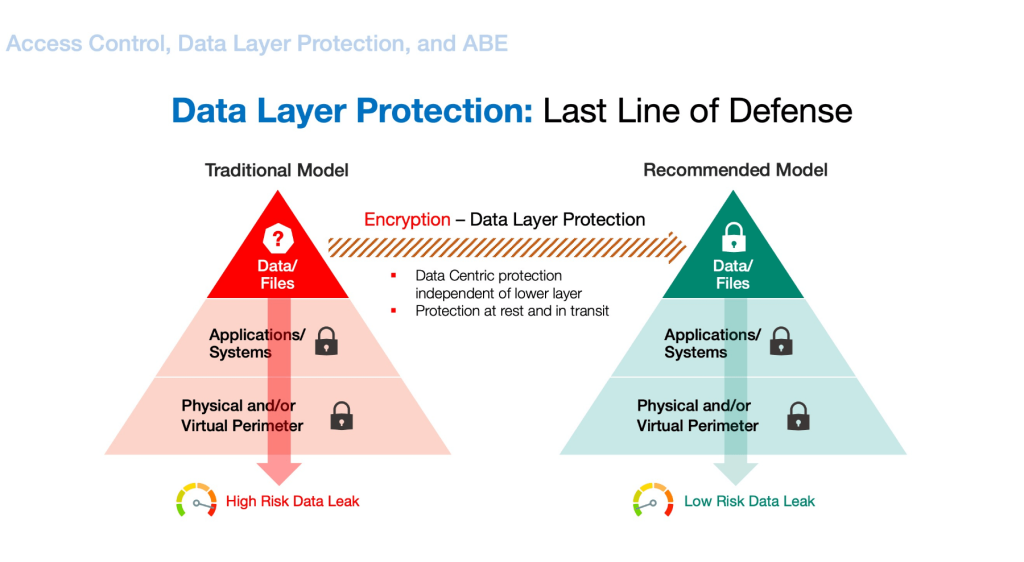
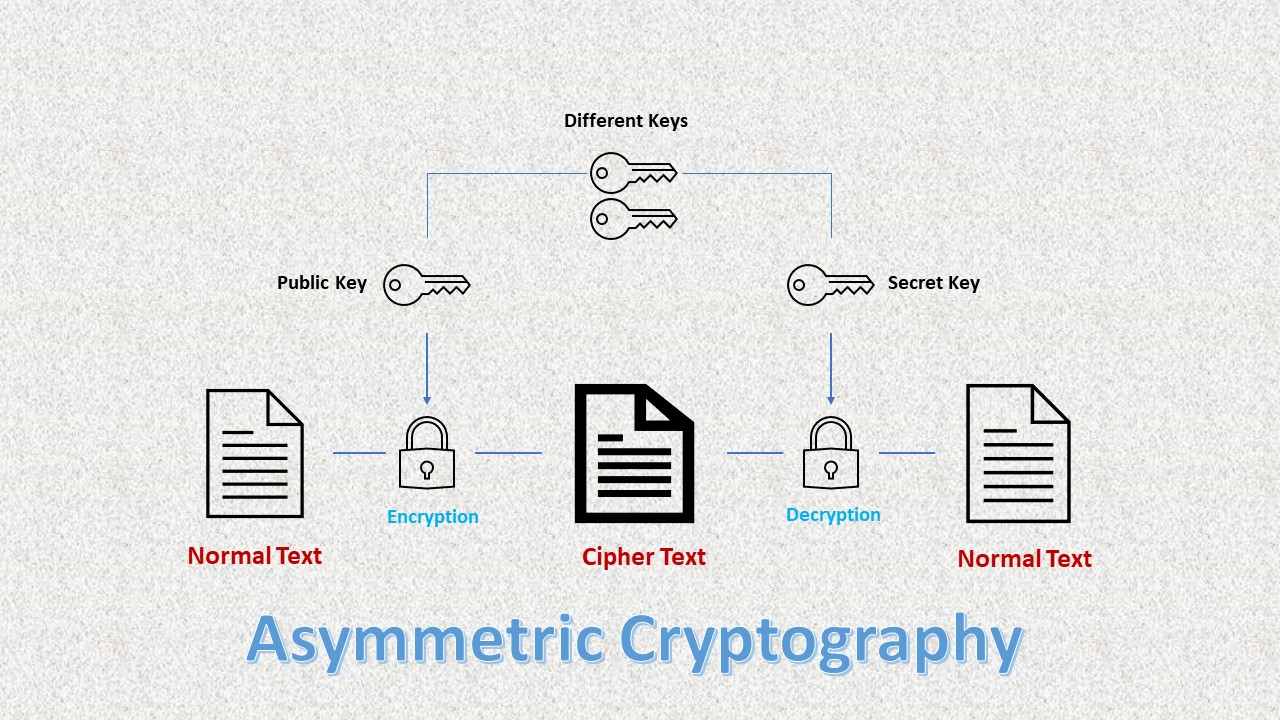
Cryptographic access control uses cryptographic techniques to protect data and control access to resources. | by Dale Clifford | Internet Stack | Jan, 2024 | Medium
Adaptive Cryptographic Access Control von Anne V. D. M. Kayem, Selim G. Akl und Patrick Martin | ISBN 978-1-4419-6654-4 | Buch online kaufen -

Online Course: OWASP Top 10: #1 Broken Access Control and #2 Cryptographic Failures from LinkedIn Learning | Class Central

A novel hybrid cryptographic framework for secure data storage in cloud computing: Integrating AES-OTP and RSA with adaptive key management and Time-Limited access control - ScienceDirect

![PDF] Hybrid Cryptographic Access Control for Cloud-Based EHR Systems | Semantic Scholar PDF] Hybrid Cryptographic Access Control for Cloud-Based EHR Systems | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/dffbb4fd8d05fa9a844c22f09ee85abb11e956aa/2-Figure1-1.png)









![MS-STOROD]: Encrypted File Access Control and Encryption | Microsoft Learn MS-STOROD]: Encrypted File Access Control and Encryption | Microsoft Learn](https://learn.microsoft.com/en-us/openspecs/windows_protocols/ms-storod/ms-storod_files/image007.png)